Official 2014 Latest Microsoft 70-412 Exam Dump Free Download(301-310)!
QUESTION 301
Hotspot Question
You have a server named Server1 that runs Windows Server 2012 R2.
You are configuring a storage space on Server1.
You need to ensure that the storage space supports tiered storage.
Which settings should you configure?
To answer, select the appropriate options in the answer area.
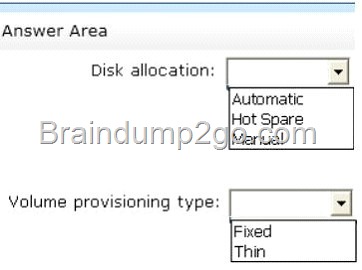
Answer:
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image0014_thumb.jpg)
QUESTION 302
Hotspot Question
You have a server that runs Windows Server 2012 R2 and has the iSCSI Target Server role service installed.
You run the New-IscsiVirtualDisk cmdlet as shown in the New-IscsiVirtualDisk exhibit.
(Click the Exhibit button.)
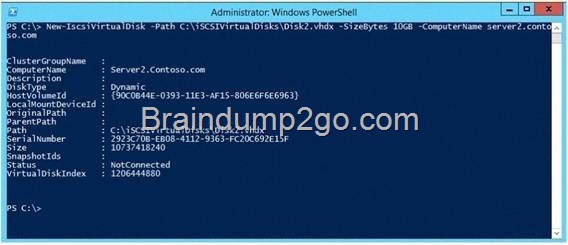
To answer, complete each statement according to the information presented in the exhibits.
Each correct selection is worth one point.
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image0016_thumb.jpg)
Answer:
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image0018_thumb.jpg)
QUESTION 303
Your network contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Active Directory Certificate Services server role installed and is configured as a standalone certification authority (CA).
You install a second server named Server2. You install the Online Responder role service on Server2.
You need to ensure that Server1 can issue an Online Certificate Status Protocol (OCSP) Response Signing certificate to Server2.
What should you run on Server1?
A. The certreq.exe command and specify the -policy parameter
B. The certutil.exe command and specify the -getkey parameter
C. The certutil.exe command and specify the -setreg parameter
D. The certreq.exe command and specify the -retrieve parameter
Answer: C
QUESTION 304
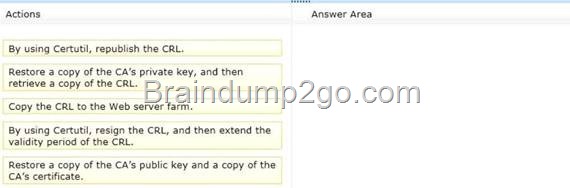
Drag and Drop Question
Your network contains two Active Directory forests named contoso.com and adatum.com. Each forest contains an Active Directory Rights Management Services (AD RMS) root cluster. All servers run Windows Server 2012 R2.
You need to ensure that the rights account certificates issued in adatum.com are accepted by the AD RMS root cluster in contoso.com.
What should you do in each forest?
To answer, drag the appropriate actions to the correct forests. Each action may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image0024_thumb.jpg)
Answer:
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image0026_thumb.jpg)
QUESTION 305
Your network contains an Active Directory domain named contoso.com. All servers run Windows Server 2012 R2.
The domain contains a domain controller named DC1 that is configured as an enterprise root certification authority (CA).
All users in the domain are issued a smart card and are required to log on to their domain- joined client computer by using their smart card.
A user named User1 resigned and started to work for a competing company.
You need to prevent User1 immediately from logging on to any computer in the domain. The solution must not prevent other users from logging on to the domain.
Which tool should you use?
A. Active Directory Users and Computers
B. Active Directory Sites and Services
C. The Certificates snap-in
D. Server Manager
Answer: A
Explanation:
Disabling or enabling a user account
To open Active Directory Users and Computers, click Start , click Control Panel , double-click Administrative Tools , and then double-click Active Directory Users and Computers .
To open Active Directory Users and Computers in Windows Server 2012, click Start , type dsa.msc .
In the console tree, click Users .
In the details pane, right-click the user.
Depending on the status of the account, do one of the following:
To disable the account, click Disable Account .
To enable the account, click Enable Account .
QUESTION 306
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs a Server Core installation of Windows Server 2012 R2.
You need to deploy a certification authority (CA) to Server1. The CA must support the auto- enrollment of certificates.
Which two cmdlets should you run? (Each correct answer presents part of the solution.
Choose two.)
A. Add-CAAuthoritylnformationAccess
B. Install-AdcsCertificationAuthority
C. Add-WindowsFeature
D. Install-AdcsOnlineResponder
E. Install-AdcsWebEnrollment
Answer: BE
Explanation:
* The Install-AdcsCertificationAuthority cmdlet performs installation and configuration of the AD CS CA role service.
*The Install-AdcsWebEnrollment cmdlet performs initial installation and configuration of the Certification Authority Web Enrollment role service.
QUESTION 307
Your network contains an Active Directory domain named contoso.com. The domain contains a server named Server1 that runs Windows Server 2012 R2. Server1 has the Active Directory Rights Management Services server role installed.
The domain contains a domain local group named Group1.
You create a rights policy template named Template1. You assign Group1 the rights to Template1.
You need to ensure that all the members of Group1 can use Template1.
What should you do?
A. Configure the email address attribute of Group1.
B. Convert the scope of Group1 to global.
C. Convert the scope of Group1 to universal.
D. Configure the email address attribute of all the users who are members of Group1.
Answer: D
QUESTION 308
You have a server named Server1 that runs Windows Server 2012 R2.
From Server Manager, you install the Active Directory Certificate Services server role on
Server1.
A domain administrator named Admin1 logs on to Server1.
When Admin1 runs the Certification Authority console, Admin1 receive the following error message.
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image00110_thumb.jpg)
You need to ensure that when Admin1 opens the Certification Authority console on Server1, the error message does not appear.
What should you do?
A. Run the Install-AdcsCertificationAuthority cmdlet.
B. Install the Active Directory Certificate Services (AD CS) tools.
C. Modify the PATH system variable.
D. Add Admin1 to the Cert Publishers group.
Answer: B
QUESTION 309
Your network contains an Active Directory forest named contoso.com. The forest contains four domains. All servers run Windows Server 2012 R2.
Each domain has a user named User1.
You have a file server named Server1 that is used to synchronize user folders by using the
Work Folders role service.
Server1 has a work folder named Sync1.
You need to ensure that each user has a separate folder in Sync1.
What should you do?
A. From Windows Explorer, modify the Sharing properties of Sync1.
B. Run the Set-SyncServerSetting cmdlet.
C. From File and Storage Services in Server Manager, modify the properties of Sync1.
D. Run the Set-SyncShare cmdlet.
Answer: D
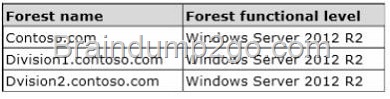
QUESTION 310
Hotspot Question
Your network contains an Active Directory domain named contoso.com. The relevant servers in the domain are configured as shown in the following table.
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image00112_thumb.jpg)
You plan to create a shared folder on Server1 named Share1. Share1 must only be accessed by users who are using computers that are joined to the domain.
You need to identify which servers must be upgraded to support the requirements of Share1.
In the table below, identify which computers require an upgrade and which computers do not require an upgrade. Make only one selection in each row. Each correct selection is worth one point.
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image00114_thumb.jpg)
Answer:
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_CC73/clip_image00116_thumb.jpg)
Passing Microsoft 70-412 Exam successfully in a short time! Just using Braindump2go’s Latest Microsoft 70-412 Dump: http://www.braindump2go.com/70-412.html
![clip_image002[18] clip_image002[18]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00218_thumb.jpg)
![clip_image002[20] clip_image002[20]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00220_thumb.jpg)
![clip_image002[22] clip_image002[22]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00222_thumb.jpg)
![clip_image002[24] clip_image002[24]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00224_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00114_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00116_thumb.jpg)
![clip_image002[26] clip_image002[26]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00226_thumb.jpg)
![clip_image002[28] clip_image002[28]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00228_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0018_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00212_thumb.jpg)
![clip_image002[14] clip_image002[14]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00214_thumb.jpg)
![clip_image002[16] clip_image002[16]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00216_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image00110_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0024_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0014_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/80b5919b6779_9DBD/clip_image0028_thumb.jpg)
![clip_image001[62] clip_image001[62]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00162_thumb.jpg)
![clip_image001[64] clip_image001[64]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00164_thumb.jpg)
![clip_image001[66] clip_image001[66]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00166_thumb.jpg)
![clip_image001[68] clip_image001[68]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00168_thumb.jpg)
![clip_image001[70] clip_image001[70]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00170_thumb.jpg)
![clip_image001[72] clip_image001[72]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00172_thumb.jpg)
![clip_image001[74] clip_image001[74]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00174_thumb.jpg)
![clip_image001[76] clip_image001[76]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00176_thumb.jpg)
![clip_image001[78] clip_image001[78]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00178_thumb.jpg)
![clip_image001[80] clip_image001[80]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00180_thumb.jpg)
![clip_image001[82] clip_image001[82]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00182_thumb.jpg)
![clip_image001[84] clip_image001[84]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00184_thumb.jpg)
![clip_image001[86] clip_image001[86]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00186_thumb.jpg)
![clip_image001[88] clip_image001[88]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00188_thumb.jpg)
![clip_image001[90] clip_image001[90]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00190_thumb.jpg)
![clip_image002[10] clip_image002[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00210_thumb.jpg)
![clip_image002[12] clip_image002[12]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00212_thumb.jpg)
![clip_image001[92] clip_image001[92]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00192_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00122_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00124_thumb.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00126_thumb.jpg)
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00128_thumb.jpg)
![clip_image001[30] clip_image001[30]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00130_thumb.jpg)
![clip_image001[32] clip_image001[32]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00132_thumb.jpg)
![clip_image001[34] clip_image001[34]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00134_thumb.jpg)
![clip_image001[36] clip_image001[36]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00136_thumb.jpg)
![clip_image001[38] clip_image001[38]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00138_thumb.jpg)
![clip_image001[40] clip_image001[40]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00140_thumb.jpg)
![clip_image001[42] clip_image001[42]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00142_thumb.jpg)
![clip_image001[44] clip_image001[44]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00144_thumb.jpg)
![clip_image001[46] clip_image001[46]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00146_thumb.jpg)
![clip_image001[48] clip_image001[48]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00148_thumb.jpg)
![clip_image001[50] clip_image001[50]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00150_thumb.jpg)
![clip_image001[52] clip_image001[52]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00152_thumb.jpg)
![clip_image001[54] clip_image001[54]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00154_thumb.jpg)
![clip_image001[56] clip_image001[56]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00156_thumb.jpg)
![clip_image001[58] clip_image001[58]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00158_thumb.jpg)
![clip_image001[60] clip_image001[60]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00160_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0016_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00112_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00114_thumb.jpg)
![clip_image002[4] clip_image002[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0024_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00116_thumb.jpg)
![clip_image002[6] clip_image002[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0026_thumb.jpg)
![clip_image002[8] clip_image002[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image0028_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-414-Ex_7993/clip_image00118_thumb.jpg)
![clip_image001[18] clip_image001[18]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00118_thumb.jpg)
![clip_image002[33] clip_image002[33]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00233_thumb.jpg)
![clip_image002[35] clip_image002[35]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00235_thumb.jpg)
![clip_image002[37] clip_image002[37]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00237_thumb.jpg)
![clip_image002[39] clip_image002[39]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00239_thumb.jpg)
![clip_image001[20] clip_image001[20]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00120_thumb.jpg)
![clip_image001[22] clip_image001[22]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00122_thumb.jpg)
![clip_image001[24] clip_image001[24]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00124_thumb.jpg)
![clip_image001[26] clip_image001[26]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00126_thumb.jpg)
![clip_image002[41] clip_image002[41]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00241_thumb.jpg)
![clip_image001[28] clip_image001[28]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00128_thumb.jpg)
![clip_image001[30] clip_image001[30]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00130_thumb.jpg)
![clip_image001[32] clip_image001[32]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00132_thumb.jpg)
![clip_image001[34] clip_image001[34]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00134_thumb.jpg)
![clip_image002[17] clip_image002[17]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00217_thumb.jpg)
![clip_image002[19] clip_image002[19]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00219_thumb.jpg)
![clip_image002[21] clip_image002[21]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00221_thumb.jpg)
![clip_image002[23] clip_image002[23]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00223_thumb.jpg)
![clip_image001[16] clip_image001[16]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00116_thumb.jpg)
![clip_image002[25] clip_image002[25]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00225_thumb.jpg)
![clip_image002[27] clip_image002[27]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00227_thumb.jpg)
![clip_image002[29] clip_image002[29]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00229_thumb.jpg)
![clip_image002[31] clip_image002[31]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00231_thumb.jpg)
![clip_image001[8] clip_image001[8]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0018_thumb.jpg)
![clip_image001[10] clip_image001[10]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00110_thumb.jpg)
![clip_image001[12] clip_image001[12]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00112_thumb.jpg)
![clip_image002[5] clip_image002[5]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0025_thumb.jpg)
![clip_image002[7] clip_image002[7]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0027_thumb.jpg)
![clip_image001[14] clip_image001[14]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00114_thumb.jpg)
![clip_image002[9] clip_image002[9]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0029_thumb.jpg)
![clip_image002[11] clip_image002[11]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00211_thumb.jpg)
![clip_image002[13] clip_image002[13]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00213_thumb.jpg)
![clip_image002[15] clip_image002[15]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image00215_thumb.jpg)
![clip_image002[1] clip_image002[1]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0021_thumb.jpg)
![clip_image002[3] clip_image002[3]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0023_thumb.jpg)
![clip_image001[4] clip_image001[4]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0014_thumb.jpg)
![clip_image001[6] clip_image001[6]](http://examgod.com/l2pimages/Official-2014-Latest-Microsoft-70-412-Ex_A7C2/clip_image0016_thumb.jpg)